Configure a Microsoft CA
To configure a Microsoft Certificate Authority (Microsoft CA), you must complete procedures on two different machines.
-
Microsoft CA—The Microsoft CA is located on a Domain Computer or Domain Controller. For additional details on Microsoft certificate authorities see: https://docs.microsoft.com/en-us/windows/win32/seccertenroll/about-certification-authorities
noteIdentity as a Service supports only Microsoft Enterprise CA.
-
Microsoft CA Proxy Server—The interfacing component that communicates to the Microsoft CA. This component must be deployed on a domain-joined machine in the same domain as the Microsoft CA.
If you are publishing certificates to Active Directory, the subject dn of your generated certificates must correctly identify the associated user in Active Directory. If you are using AD Sync to sync users to Identity as a Service, the certificate subject DN is automatically set with the user's DN. See Configure a DN attribute for Microsoft CA.
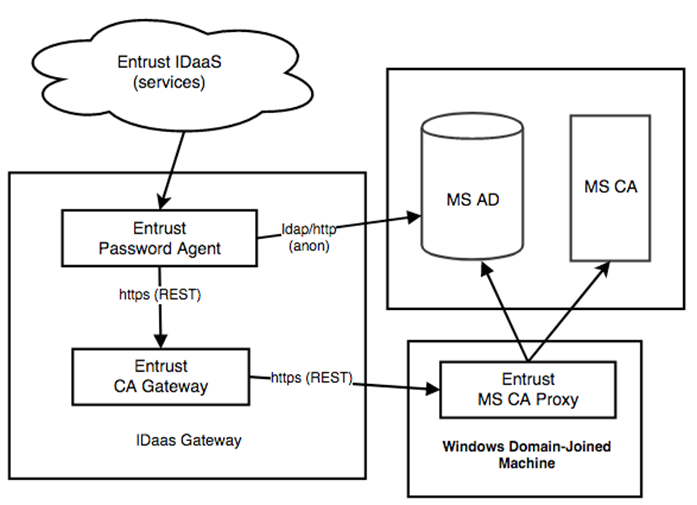
Overview
The use of a Microsoft CA with Identity as a Service involves the following components and interactions:
Prerequisites
Before you begin, you need a machine that will host the Microsoft Certification Authority Proxy with the following:
- Windows Server 2016 (x64) and above
- Java 11 version or later of Oracle Java, OpenJDK, or AdoptOpenJDK. To check the Java installation, run java -version
- Install the Microsoft CA Proxy on the Microsoft CA Proxy Server.
- The domain user account is used by the MSCA Proxy to access MSCA.
- The CA configuration gives permissions to the domain user account to issue and manage certificates and request certificates.
- All templates used by IDaaS allow the domain user to read and enroll certificates.
- Permissions against authenticated users are reduced or restricted.
- Permissions against all other users and roles are managed by the CA operator.
Create a domain user account
You need to create a domain administrator account with the following Certificate Authority permissions:
When you create the domain user, the user has a domain user membership. Add the cert publisher membership to this domain user. You can give the domain user any name. Set the password and expiry rules as required by your policy.
- Create a domain user account.
- Set the Certificate Authority permissions.
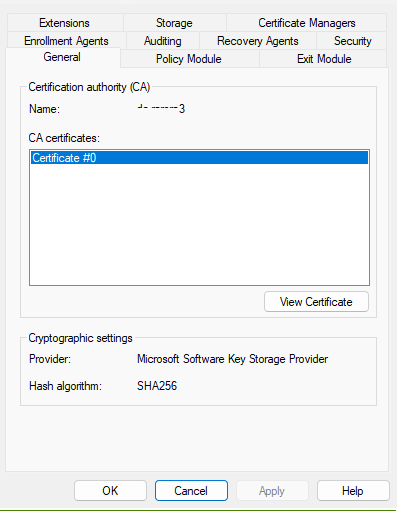
- On the Microsoft CA machine, go to Start > Windows Administrative Tools > Certification Authority.
- Right-click the Certification Authority and select Properties. The CA Properties dialog box appears.
- Click the Security tab.
- In the Group or user names list, add the new domain user to the list.
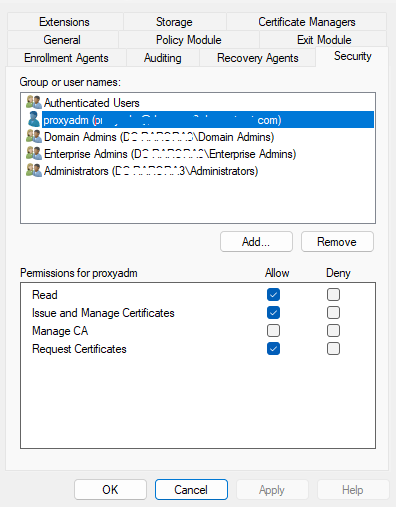
- Under Permissions for
<user domain_user>, in the Allow column, ensure that the following permissions are selected:- Read
- Issue and Manage Certificates
- Request Certificates
- Click Apply to save the settings and close the window.
- Review the permissions for other users and groups in the list to make sure they follow your corporate access policy.
Upgrade to Microsoft Proxy 2.7.10
-
Go to the directory where Microsoft CA Proxy 2.5.4 is installed (for example, c:\mscaproxy).
-
Run the following command as an administrator:
MSCAProxy stopMSCAProxy uninstall -
Rename the Microsoft CA Proxy 2.5.4 directory as follows:
move c:\mscaproxy c:\mscaproxy2.5.4noteIf you get an error accessing the files, perform a reboot and run the command again to move the files.
Install the Microsoft CA Proxy 2.7.10
-
Download the Microsoft CA Proxy server installation file form Identity as a Service:
- Click > Resources > Gateways. The Gateways page appears.
- Click Microsoft CA Proxy. The Microsoft CA Proxy Download URL dialog box appears.
- In the Microsoft CA Proxy Download URL dialog box, click Microsoft CA Proxy to download the
msca-proxy-install-2.7.10-158.zipfile.
-
Copy the
msca-proxy-install-2.7.10-158.zipfile to your Microsoft CA Proxy server machine. -
Unzip the contents of the compressed file in a local directory of the Windows machine (for example,
c:\mscaproxy). -
Run the following command as an administrator:
MSCAProxy install /pinfoThe /p option is required in order to be prompted to use a domain user account with the required permissions as mentioned below.
-
At the username and password prompt, use the domain user with the following permissions on the CA.
noteWhen entering the domain user, the value should be of the form
domain\username, for example,mydomain\<domain_user>.
Complete the Microsoft CA Proxy 2.7.10 upgrade
-
Do the following to maintain the existing ssl keys, certificates, and configuration:
xcopy c:\mscaproxy2.5.4\config\* c:\mscaproxy\config /Ixcopy c:\mscaproxy2.5.4\ssl\* c:\mscaproxy\ssl /Ixcopy c:\mscaproxy2.5.4\tmp\* c:\mscaproxy\tmp /I (or xcopy c:\mscaproxy\client\* c:\mscaproxy\client /I) -
Update the keystore and truststore passwords. These will be re-encrypted using the latest MSCA Proxy version.
- Go to
<msca_install\>/configand openkey-store-password.scrtwith a text editor. - Change
encrypted=<encrypted-keystorepwd>todecrypted=<keystorepwd>where<decrypted-keystorepwd>is the decrypted password of the JKS keystore used with the Microsoft CA Proxy Server. - Save and close the file.
- Go to
<msca_install\>/configand opentrust-store-password.scrtwith a text editor. - Change
encrypted=<encrypted-truststorepwd>todecrypted=<decrypted-truststorepwd>where<decrypted-truststorepwd>is the decrypted password of the JKS truststore used with the Microsoft CA Proxy Server. - Save and close the file.
- Go to
-
As an administrator, run the following command:
MSCAProxy start
There are many topics in this section. It is important that you complete the procedures in the following order:
Create a Microsoft CA Enrollment Agent
You need an Enrollment agent to publish a certificate in Active Directory.
Create a Microsoft CA Key Recovery Agent
You need a Key Recovery agent to perform a key recovery operation.
Configure Microsoft CA for PIV certificate templates
7 items
Configure Microsoft CA Proxy
Complete the following to configure the Microsoft CA Proxy:
Create PIV CS PKCS12 store (PIV PFX)
1. Create a new user in Active Directory, as follows:
Configure a Microsoft CA in IDaaS
Before you begin this procedure, ensure that you have completed all the previous steps in this section, Configure a Microsoft CA. This procedure outlines how to configure a Microsoft CA in Identity as a Service. You need to upload the certificate and key files that you created in earlier sections.
Edit, refresh, and test a Microsoft CA
If you make changes to the Microsoft Certification Authority, in Identity as a Service you must refresh the Microsoft CA to ensure that the Microsoft CA Gateway picks up the latest configuration changes. This is particular necessary if changes are made to the configuration of the Certification Authority, for example, editing certificate templates. If you need to make changes to your Microsoft CA in Identity as a Service, for example, change the Microsoft Proxy Server certification, you can edit and save the changes. You can also test the connection to your Microsoft CA to help troubleshoot connection issues.
Configure a certificate subject DN attribute for Microsoft CA
Identity as a Service supports a user DN if you want to publish certificates to Active Directory.
Export a Microsoft CA trust chain
You must export a user's smart credential certificate authority to their Windows Domain if a user wants to use their smart credential for Windows Smart Card Logon (SCLO). The CA certificates exported from an Identity as a Service account are contained in a zip file. The zip file contains the following files: